DevOps Industry Updates #2
Hi everyone, welcome to the 2nd issue of my DevOps Industry Updates newsletter. While there is a lot of turbulence in our world right now, one thing that I think will continue to unite us is our shared passion to build great things.
🔥 Top Cream
This issue’s top 4 stories:
- How Cloudflare uses HashiCorp Nomad
- django-postgres-vue-gitlab-ecs
- How we reduced the AWS costs of our streaming data pipeline by 67%
- Zero-day in Sign in with Apple
🌎 Society

- Slack and AWS join forces to drive agility in software development by Slack Blog: Slack will draw on the underlying tech for Chime video-calling service to deliver better video calls for millions of Slack users, employees of Amazon will be able to use Slack.

- Priyanka Sharma takes over the leadership of the CNCF by Frederic Lardinois: the Cloud Native Computing Foundation, the Linux Foundation-based home of open-source projects like Kubernetes, OpenTracing and Envoy, today announced that Dan Kohn is stepping down and Priyanka Sharma (director of Cloud Native Alliances at GitLab) will be stepping into the general manager role.
- DigitalOcean Raises $50M At $1.15B Valuation by Mary Ann Azevedo: DigitalOcean, which describes itself as “the cloud for developing modern apps,” announced today that it has raised a $50 million Series C at a valuation of $1.15 billion.
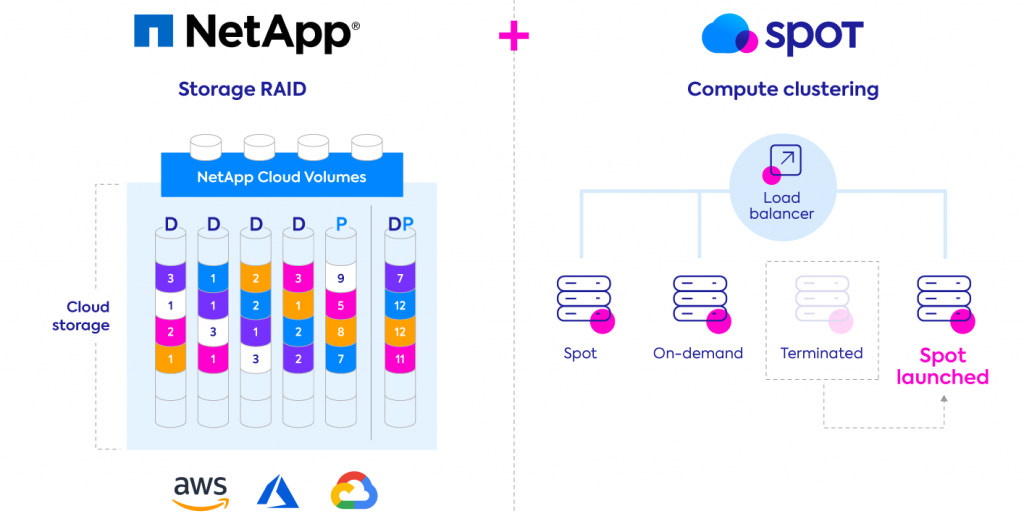
- NetApp to Acquire Spot.io: NetApp today announced it has entered into a definitive agreement to acquire Spot, a leader in compute management and cost optimization on the public clouds, to help it establish leadership in Application Driven Infrastructure.
📟 DevOps
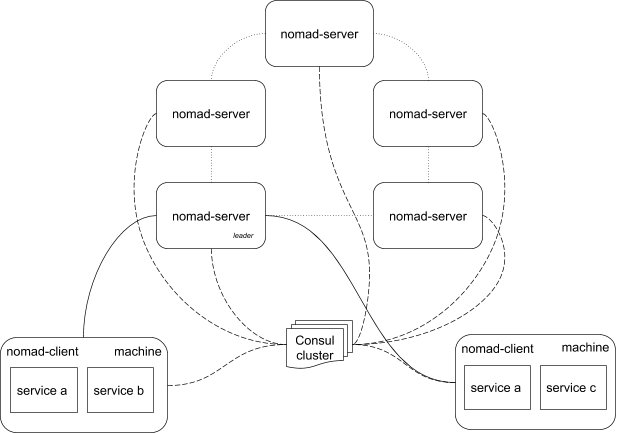
- How Cloudflare uses HashiCorp Nomad by Thomas Lefebvre: in this blog post, we will walk you through the reliability model of services running in our more than 200 edge cities worldwide, including how deploying Nomad helped us improve the availability of services in each of those data centers.
- An Introduction to Apache Airflow by Bhavani Ravi: Airflow is a platform created by the community to programmatically author, schedule, and monitor workflows.

- How to Beat the Internet Latency? by Alen Zubic: We conducted network latency tests among a large number of virtual machines provisioned around the globe. Multiple cloud providers were used. Results show that by smart routing, we may be able to build fast networks—maybe faster than the internet as we know it.

-
Log Monitoring and Alerting with Grafana Loki by Ruturaj Kadikar: provides an insight into the architectural differences of the Promtail, Loki, and, Grafana (PLG) stack compared to other logging and monitoring stacks such as Elasticsearch-FluentD-Kibana (EFK).
-
Should You Run Stateful Systems via Container Orchestration? by Erik Osterman: as with any tool, it’s the operator’s responsibility to know how to operate it. There are a lot of ways to blow one’s leg off using Kubernetes.
- Deploy Any Resource With The New Kubernetes Provider for Terraform: lets you package, deploy, and manage all Kubernetes resources, including Custom Resource Definitions, using HashiCorp Configuration Language (HCL).
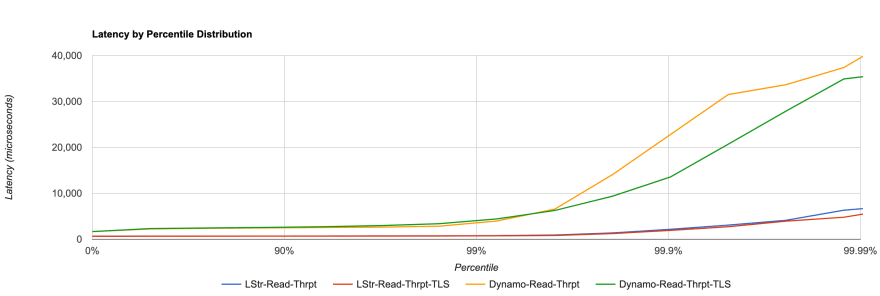
- Swifter Than DynamoDB: Lambda Store - Serverless Redis by Mattia Bianchi: as a Serverless Redis service, Lambda Store is an alternative to both DynamoDB and ElastiCache. In this post, I’ll focus on one of the cases that you should use/pick Lambda Store instead of DynamoDB.
🛠️ DevOps Tools

- SpotCost by Victor: this tool simplifies the comparison of AWS spot instances on a one-page view. Compare Pricing, interruption rate, specifications, locations, pricing in time, and between regions.
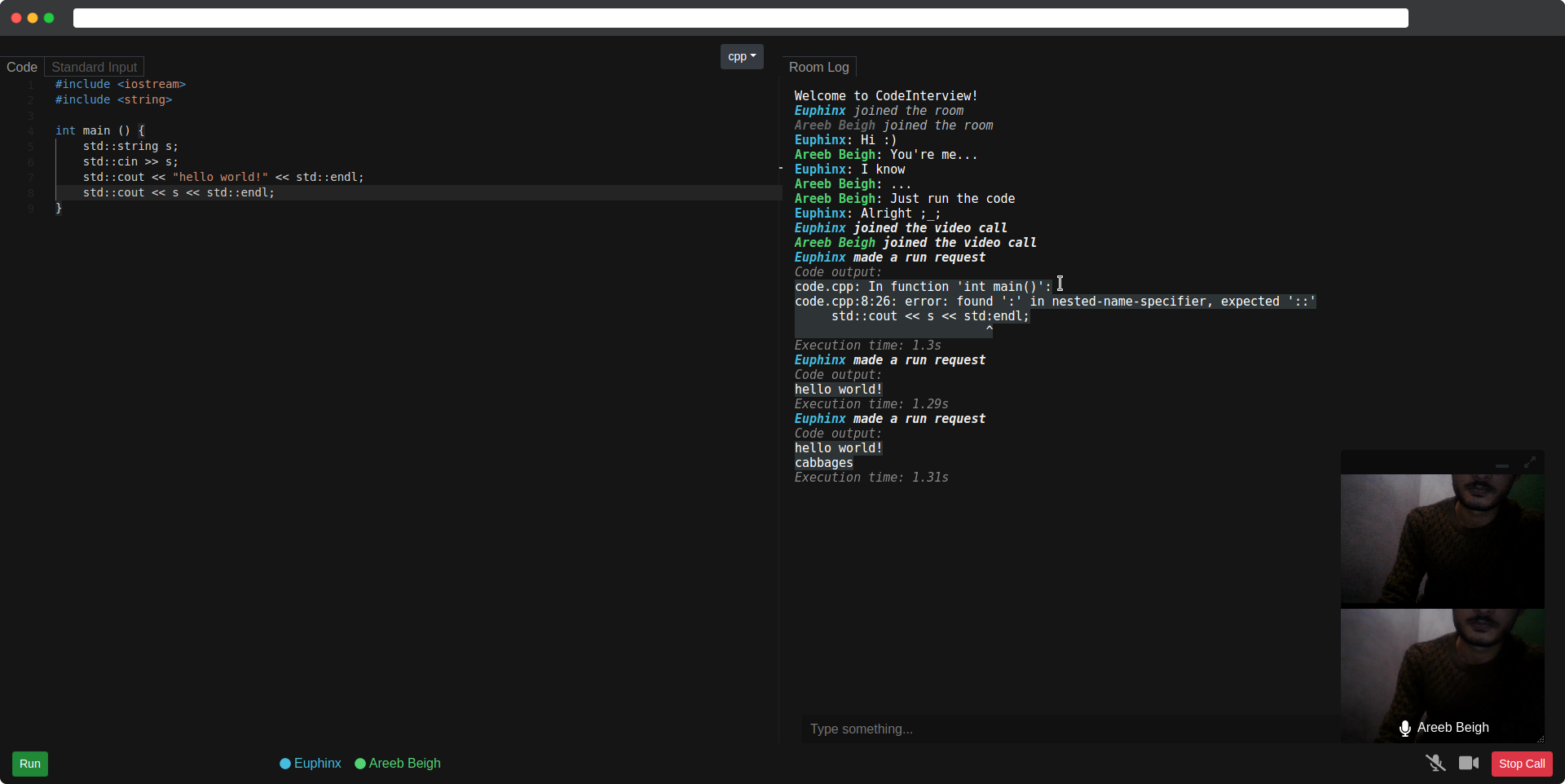
- areebbeigh/codeinterview-backend by Areeb Beigh: CodeInterview is a home made solution and personal self-learning project for online coding interviews.
- EnergizedProtection/block by Nayem Ador: consolidates several reputable filters, and merges them into a couple of protection packs with duplicates and dead/inactive domains removed. A variety of tailored packs are provided.

- The Amazon S3 challenge by Vasily Pantyukhin: through a series of levels, you’ll learn some of the Amazon S3 features.
☸️ Kubernetes
-
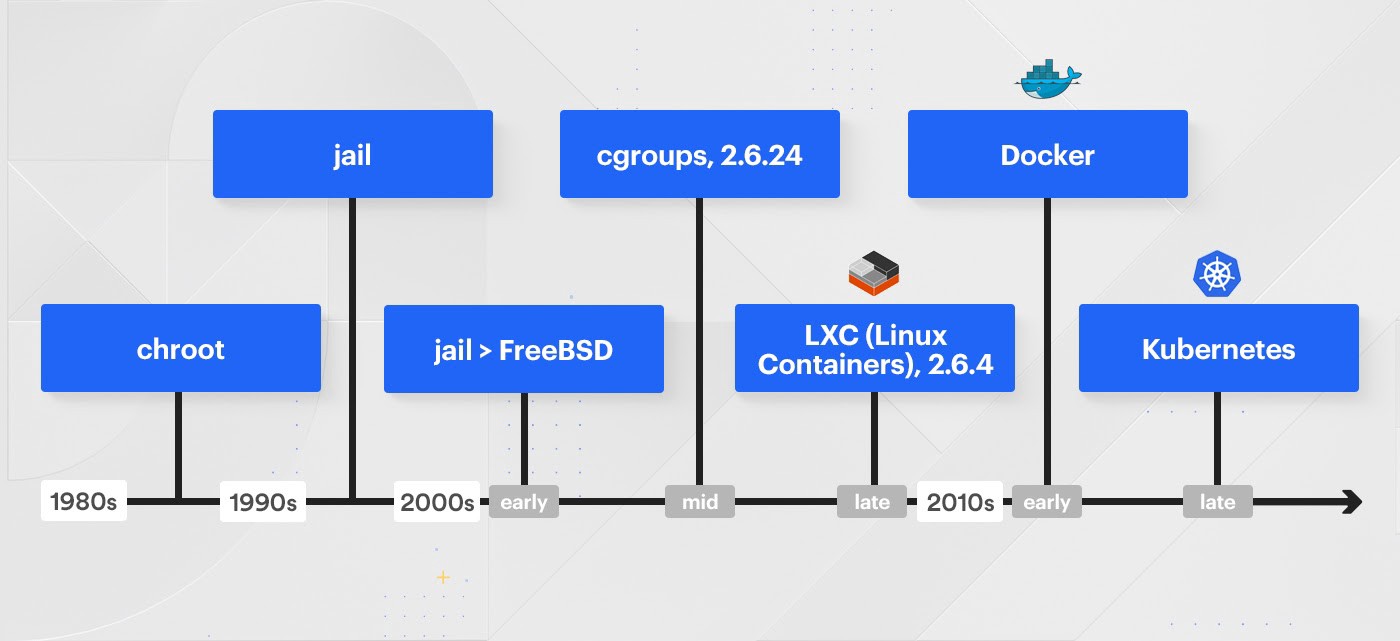
Container technologies at Coinbase: why Kubernetes is not part of our stack by Drew Rothstein: container orchestration platforms are complex and amazing technologies, helping some businesses and teams solve a whole suite of problems. What’s commonly overlooked however, is that container technologies also create a large set of challenges that must be overcome to prevent failures.
-
Why is Kubernetes getting so popular? by Ricardo Aravena: at the time of this article, Kubernetes is about six years old, and over the last two years, it has risen in popularity to consistently be one of the most loved platforms.
-
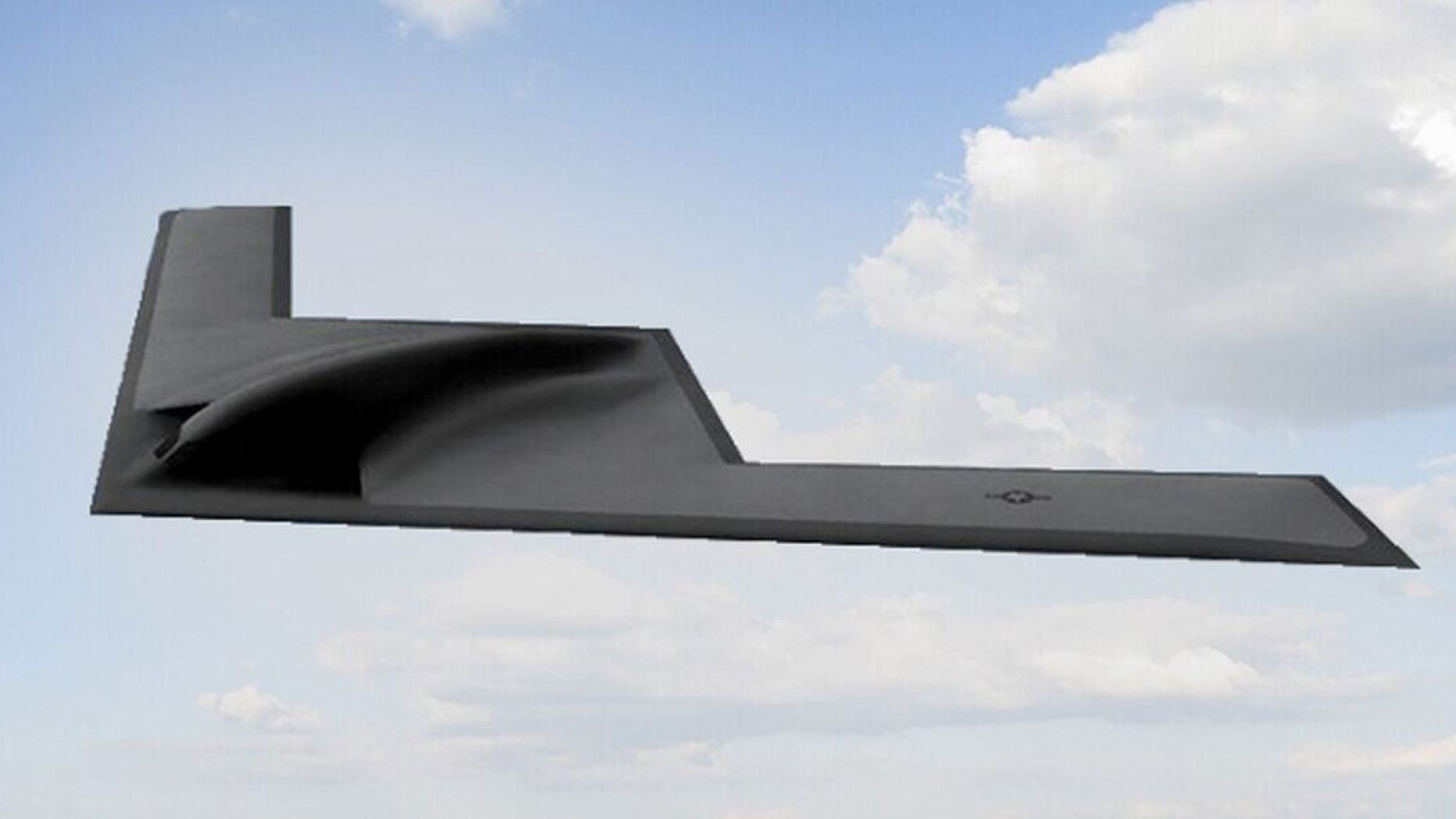
New Air Force B-21 stealth bomber runs Kubernetes by Independent Eagle: by drawing upon software-enabled virtualization, systems can upgrade faster, reduce their hardware footprint and better employ automation, AI and machine-learning applications.
-
Supporting the Evolving Ingress Specification in Kubernetes 1.18 by Alex Gervais: in this blog post, we’ll walk through what’s new in the new Ingress specification, what it means for your applications, and how to upgrade to an ingress controller that supports this new specification.
🔐 Security

- Zero-day in Sign in with Apple by Amol Baikar: what if I say, your Email ID is all I need to take over your account on your favorite website or an app. Sounds scary, right? This is what a bug in Sign in with Apple allowed me to do.

-
SHA-1 is a Shambles by Gaëtan Leurent & Thomas Peyrin: We have computed the very first chosen-prefix collision for SHA-1. In a nutshell, this means a complete and practical break of the SHA-1 hash function, with dangerous practical implications if you are still using this hash function.
-
The Impending Doom of Expiring Root CAs and Legacy Clients by Scott Helme: over the last year or so I’ve been watching as a potentially big problem has been rolling in over the horizon and just the other day I saw the first signs of the storm hitting the shore.
-
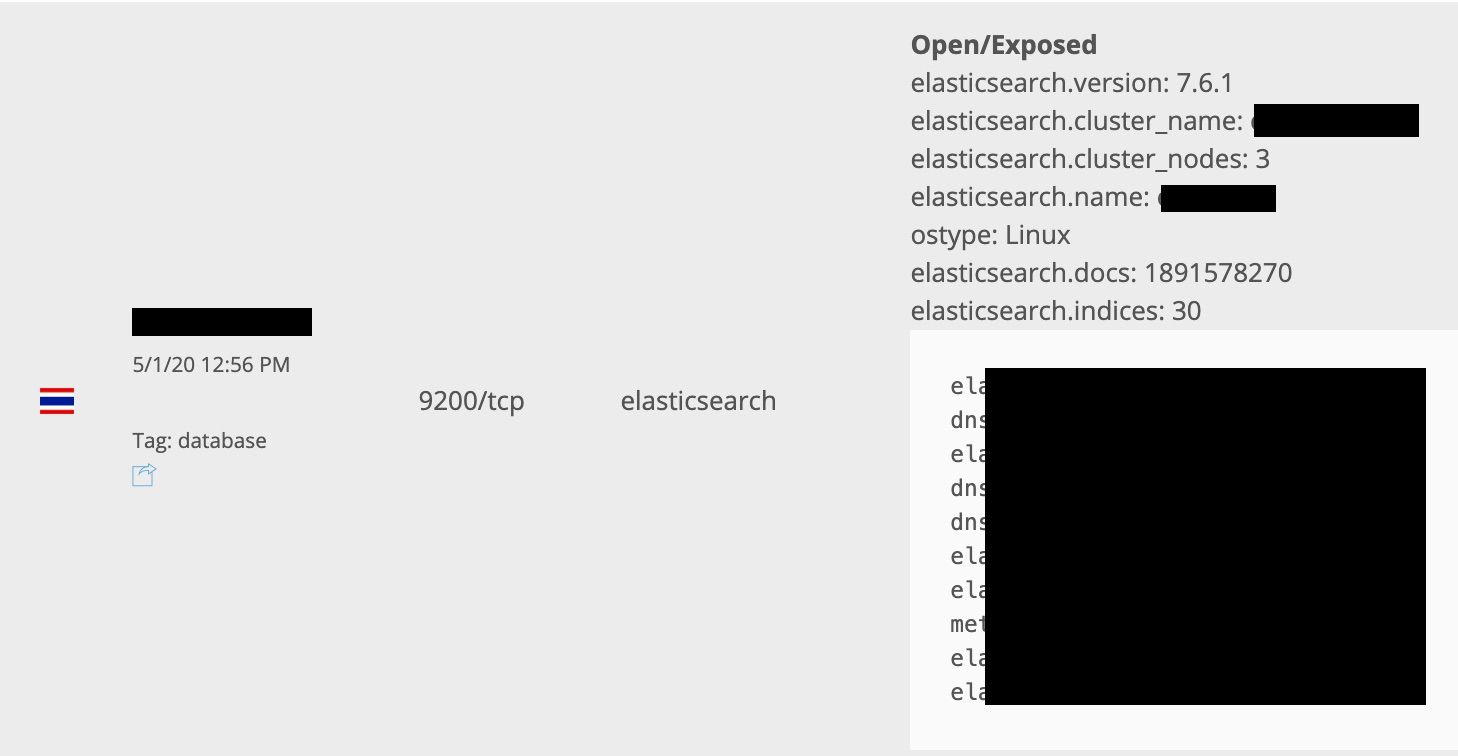
Thai Database Leaks 8.3 Billion Internet Records by xxdesmus: I recently discovered an exposed ElasticSearch database when browsing BinaryEdge and Shodan. This database appears to be owned by Thailand-based mobile network operator Advanced Info Service (AIS).
-
NSA Exposes Tool Used By Russian Hackers by William Turton: the National Security Agency publicly accused infamous Russian hacking group Sandworm of exploiting a flaw in software commonly found in Linux called “Exim”.
- (Very) Basic Intro To Elliptic Curve Cryptography by Lane Wagner: a basic introduction to elliptic curve cryptography. Assumes the audience is trying to gain an understanding of why ECC is an effective cryptographic tool and the basics of why it works.

-
Two Critical Flaws in Zoom Could’ve Let Attackers Hack Systems via Chat by Mohit Kumar: the first security vulnerability (CVE-2020-6109) resided in the way Zoom leverages GIPHY service to let its users search and exchange animated GIFs while chatting and the second remote code execution vulnerability (CVE-2020-6110) resided in the way vulnerable versions of the Zoom application process code snippets shared through the chat.
-
Weird “Subdomain Take Over” pattern of Amazon S3 by Simgamsetti Manikanta: in this write-up, I will show the non-typical way of S3 subdomain takeover and also show the OSINT process to find the s3 regions and finally how I found the correct region of the target.
💻 Programming

-
Why I’m enjoying learning Rust as a Java programmer by Mike Bursell: here are some of my thoughts on Rust, from the point of view of a Java developer with a strong object-oriented background.
-
The PEPs of Python 3.9: Python 3.9 is now feature-complete. The release announcement lists a half-dozen Python Enhancement Proposals (PEPs) that were accepted, including those for string manipulations, a new parser and more.
-
django-postgres-vue-gitlab-ecs by Brian Caffey: an example project that demonstrates local development, CI/CD and production setup for a full stack web app using Django, Django REST Framework, Django Channels, Postgres, VueJS, Redis, Celery, GitLab CI and AWS technologies deployed with CDK.
-
To Rust or not to Rust? by Liborty Rustafarian: tldr: there is no need to be afraid of Rust. When you are prepared to put some effort and application into it, it will repay you handsomely with safety and performance.
📖 Machine Learning
- Language Models are Few-Shot Learners by Cornell University: Recent work has demonstrated substantial gains on many NLP tasks and benchmarks by pre-training on a large corpus of text followed by fine-tuning on a specific task.
🐧 Linux
-
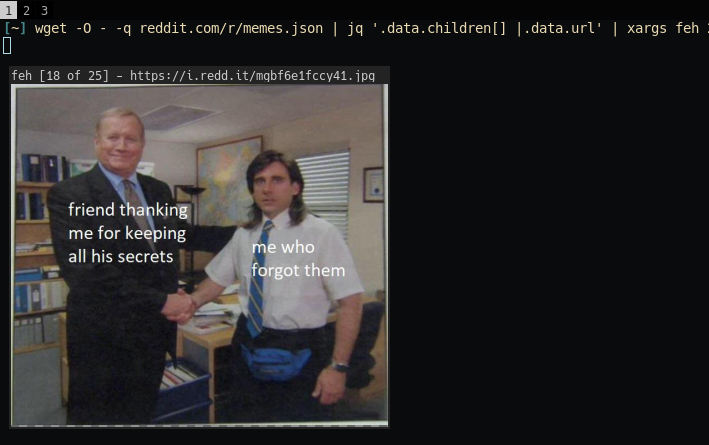
The beauty of Unix pipelines by Prithu Goswami: in this post I would like to show some examples of how one can use different unix tools together to accomplish something powerful.
-
OpenSSH 8.3 released: future deprecation notice - it is now possible to perform chosen-prefix attacks against the SHA-1 algorithm for less than USD$50K. For this reason, we will be disabling the “ssh-rsa” public key signature algorithm by default in a near-future release.
🔩 Hardware

- Reconstructing a lost NES game from 30-year-old source code disks by Rich Whitehouse: how we recovered and re-assembled Days of Thunder, an unreleased, never-before-seen title co-authored by Chris Oberth at Mindscape.
🚢 Leadership

- 5 Questions That (Newly) Virtual Leaders Should Ask Themselves by Melissa Raffoni: Melissa Raffoni, an executive coach shares five questions to ask yourself to ensure you are being the best leader you can be as you manage your team from home.
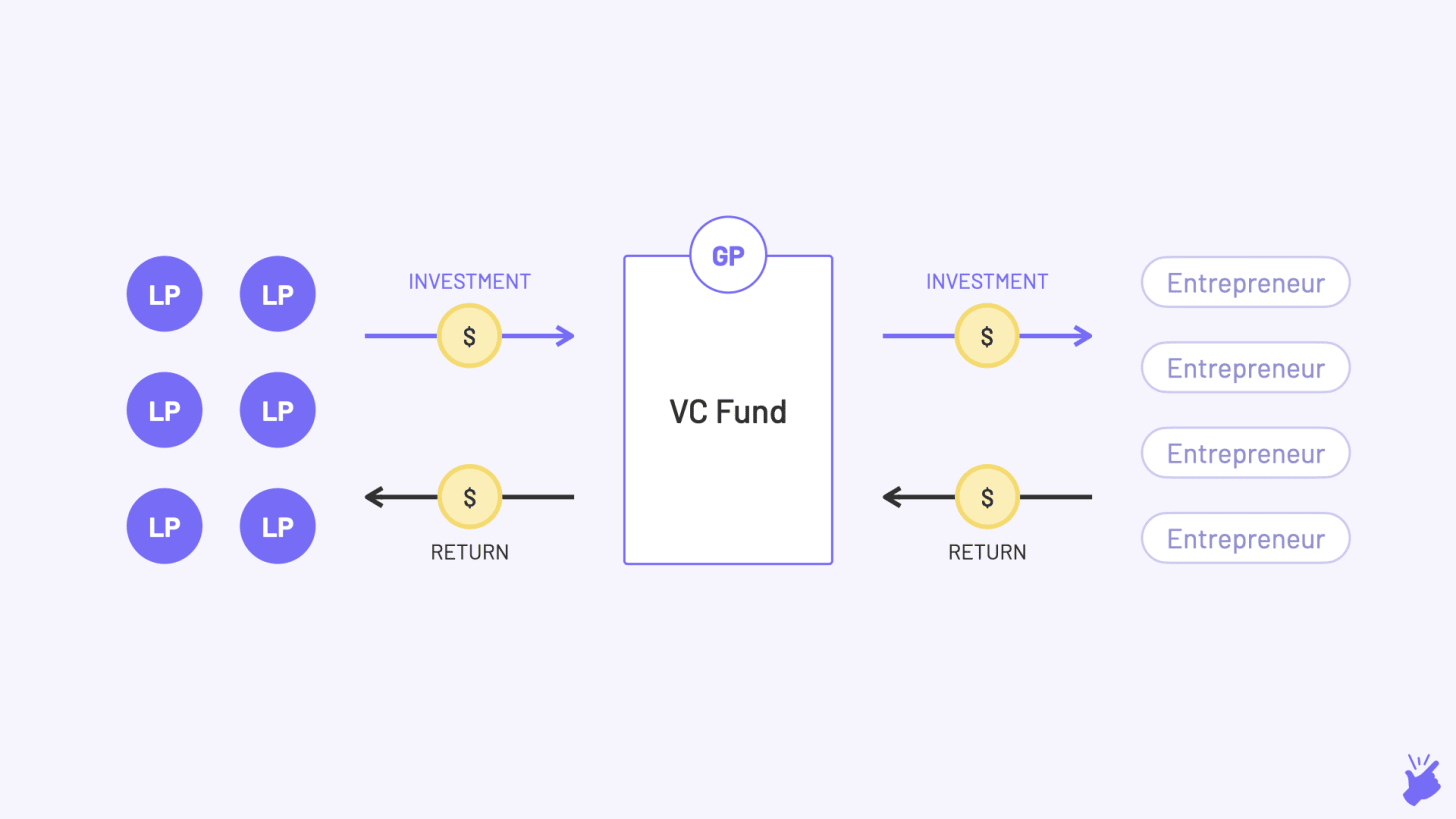
- How VC works - A Beginner’s Guide by Vivek Raju: a high-level overview of how the world of venture capital works.
☁️ Cloud
-
New ASN created for SpaceX Starlink assigned the ASN number of 14593, the combination of low latency (20-40ms) and high bandwidth (100+Mbps) has never been available in satellite internet before.
-
Container Sprawl Is the New VM Sprawl by Tobi Knaup: as organizations continue to scale and shift their operations to a hybrid mix of on-prem, cloud, and edge infrastructure, the rapid deployment of Kubernetes clusters and workloads is creating a new challenge.
AWS
- Every Amazon Web Service described in one line by Joshua Thijssen: there are 163 different Amazon Web Services - I tried to capture what the service does in a single one-liner to give you a global overview.
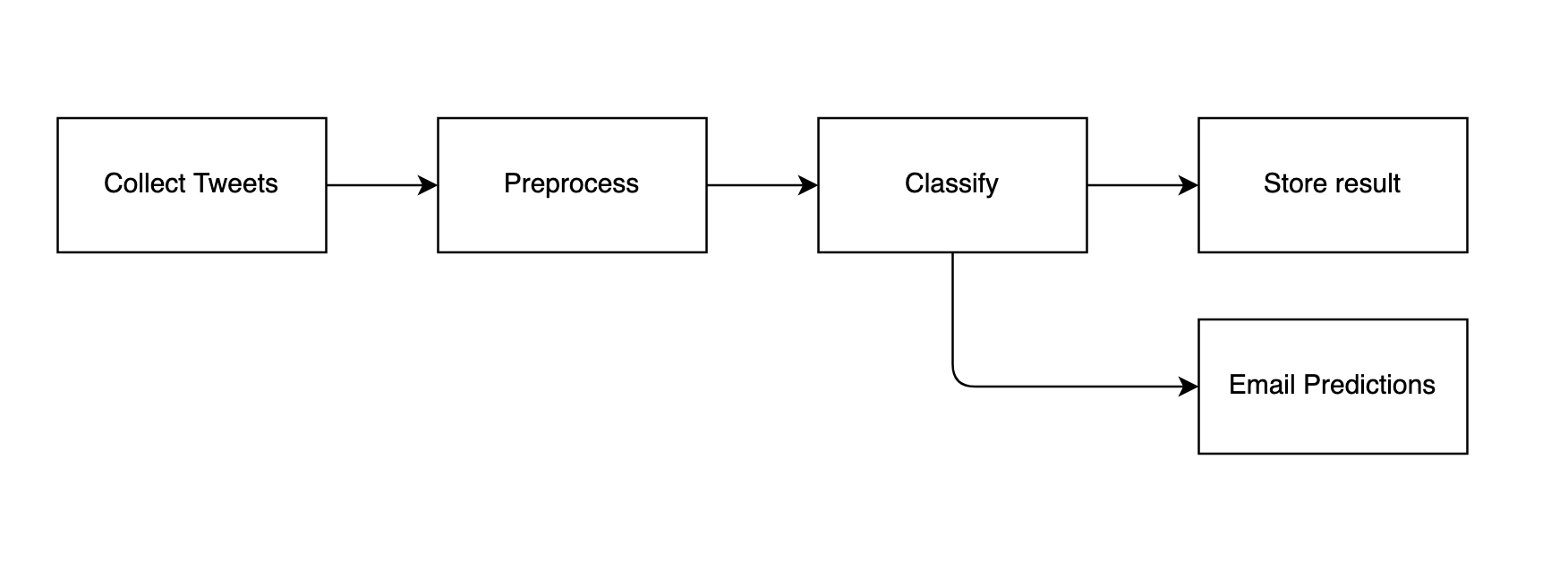
- How we reduced the AWS costs of our streaming data pipeline by 67% by Taloflow: this post illustrates how a little bit of diligence and a clear cost objective can end up making a large impact on profitability.

- Amazon EC2 C5a Instances Powered By 2nd Gen AMD EPYC Processors by Channy Yun: C5a instances are variants of Amazon EC2’s compute-optimized (C5) instance family and provide high performance processing at 10% lower cost over comparable instances. C5a instances are ideal for a broad set of compute-intensive workloads including batch processing, distributed analytics, data transformations, log analysis, and web applications.
-
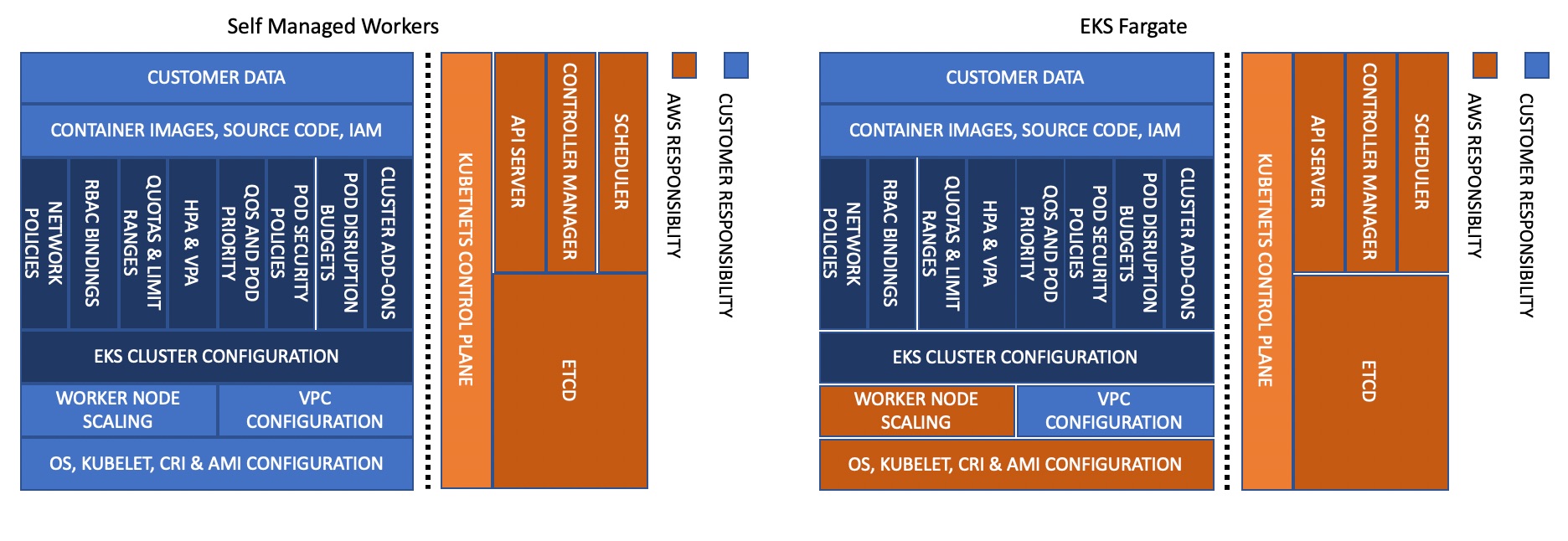
Introducing the Amazon EKS Best Practices Guide for Security: Amazon Elastic Kubernetes Service (EKS) now makes it easier to implement security best practices for Kubernetes on AWS with the Amazon EKS Best Practices Guide for Security.
-
Amazon MSK now supports Apache Kafka version upgrades: in a few clicks you can take advantage of new Apache Kafka features and bug fixes by upgrading the version of Apache Kafka deployed on new and existing Amazon Managed Streaming for Apache Kafka (Amazon MSK) clusters.

-
Single Sign-On between Okta Universal Directory and AWS by Sébastien Stormacq: how to enable automatic user synchronization between Okta and AWS, allowing users to sign in to AWS environments using the flow they are already familiar with in Okta.
-
Real-time anomaly detection support in Amazon Elasticsearch Service: Amazon Elasticsearch Service now offers anomaly detection, which uses machine learning to detect anomalies on real-time streaming data and identifies issues as they evolve so you can mitigate them immediately.
-
Tighten S3 permissions for your IAM users and roles using access history of S3 actions: to help you identify unused S3 permissions, IAM extended service last accessed information will include S3 management actions and the last time a user or role used an S3 action.
Azure
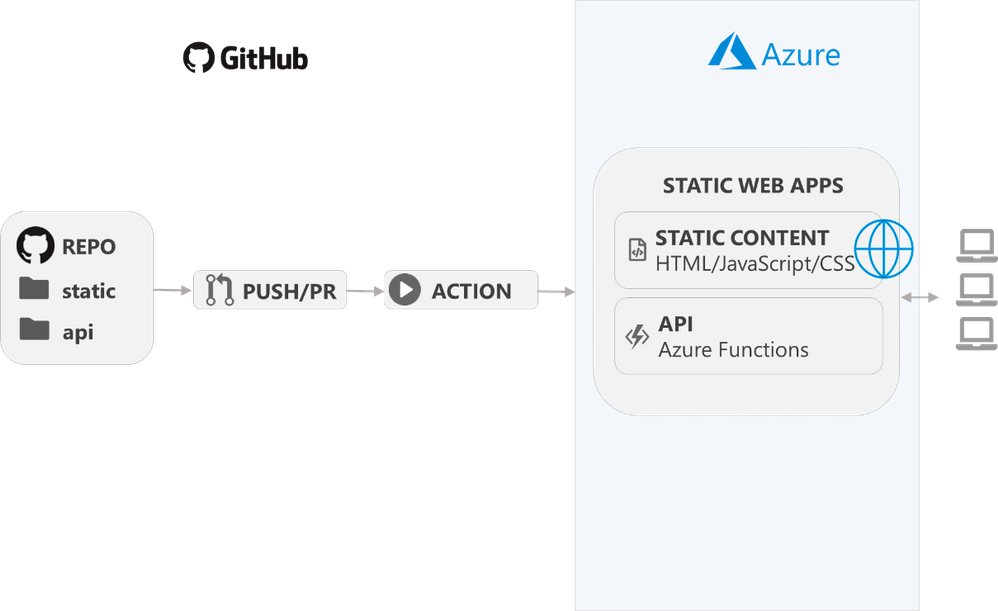
- Introducing App Service Static Web Apps by Daria Grigoriu: with Static Web Apps, developers can use modular and extensible patterns to deploy apps in minutes while taking advantage of the built-in scaling and cost-savings offered by serverless technologies.
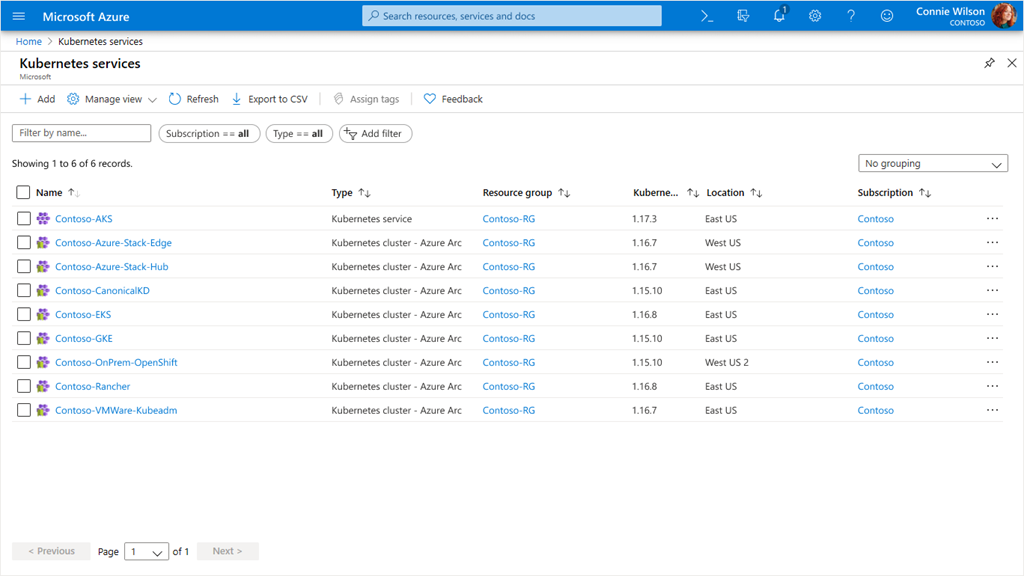
- Azure Arc enabled Kubernetes by Jeremy Winter: Azure Arc is a set of technologies that unlocks new hybrid scenarios for customers by bringing Azure services and management to any infrastructure across datacenters, edge, and multi-cloud.
GCP

- Introducing cross-region replica for Cloud SQL by Nimesh Bhagat: we are excited to launch Cloud SQL cross-region replication, which is now available for MySQL and PostgreSQL database engines.
Article version: 1.0.0


