DevOps Industry Updates #10
In this IaC-packed issue of DevOps Industry Updates, we discuss the importance of the 1x Engineer, GitHub’s new Container Registry (TL;DR: it could be the new DockerHub) and a whole lot of recent developments in the Terraform community. Grab your coffee, we have some great nuggets to cover:
🔥 Top Cream
This issue’s top 3 stories:
- The 1x Engineer
- Introducing GitHub Container Registry
- Managing multi-region, multi-account Terraform IaC
🌎 Society
- The 1x Engineer: you might have already heard of a 10x engineer. Probably too often, actually. If there’s such a thing as a 10x engineer, surely there must be a 1x engineer, too?

- DevOps engineer: IT’s most in-demand title for the future by Eveline Oehrlich: does the title “DevOps engineer” have staying power? Will it be the must-have title within IT in years to come? Should technology organizations be planning to add this role to their roster in 2021? And why is a job title in technology worth debating anyway?

- Snowflake Leads Software IPO Filing Bonanza Including Asana, JFrog, Sumo Logic, Unity Software by Alex Wilhelm: wholly IPOs Batman! After far too few startups appeared ready to take advantage of warm public market conditions and ecstatic IPO receptions, a deluge of Cloud companies have filed to go public.
📟 DevOps

- Introducing GitHub Container Registry by Kayla Ngan: an addition to the GitHub Packages feature, the GitHub Container Registry will also provide anonymous access for public container images, which it says it will provide free of charge. RIP DockerHub.
-
A comprehensive guide to managing secrets in your Terraform code by Yevgeniy Brikman: in this blog post, we’ll go over the most common techniques you can use to safely and securely manage secrets such as env vars, encrypted files and secret stores.
-
A Guide to Cloud Cost Optimization with HashiCorp Terraform by Michael Fonseca: a great overview of how to integrate and use cloud-vendor and third-party cost optimization tools in Terraform workflows. Includes examples of Terraform’s policy as code framework, Sentinel, which can automatically block overspending with rules around cost, instance types, and tags.
- CloudFormation, Terraform, or CDK? A guide to IaC on AWS by Jared Short: an answer to the age-old question: what IAC tools are available to you in AWS, and how do you choose between them?
🛠️ DevOps Tools
-
Managing multi-region, multi-account Terraform IaC by Florian Dambrine: an excellent talk that describes the practices, code patterns, as well as some tips and tricks from an old timer at GumGum. Includes a handy cheat sheet that summarizes all the technical aspects covered in the talk.
-
5 Linux network troubleshooting commands by Ricardo Gerardi: Linux provides many command-line tools to help sysadmins manage, configure, and troubleshoot network settings.
☸️ Kubernetes
-
The Runaway Problem of Kubernetes Operators and Dependency Lifecycles by Mary Branscombe: the idea of the Kubernetes operator pattern is to package up the deep knowledge about running a specific application and codify it. But operators have quickly become popular and the sheer proliferation means that ironically, teams are needing to gain deeper knowledge about operators themselves, from choosing the right operator frameworks to the operators themselves.
-
ContainerSolutions/kubernetes-examples by Ian Miell: minimal self-contained examples of standard Kubernetes features and patterns in YAML.
-
Do I Need Kubernetes? by Alex Hewson: as most things in life, it depends. This post reviews where Kubernetes shines, where it doesn’t and most importantly (IMO): cost of ownership.
🔐 Security

-
Comparing SSH Keys - RSA, DSA, ECDSA, or EdDSA? by Virag Mody: as of 2020, the most widely adopted asymmetric crypto algorithms in the PKI world are RSA, DSA, ECDSA, and EdDSA. So which one is best? Well, it depends.
-
Engineer admits he wiped 456 Cisco WebEx VMs from AWS after leaving by Thomas Claburn: Sudhish Kasaba Ramesh, who worked at Cisco from 2016 to 2018, admitted to deliberately deleting virtual machines powering Cisco’s WebEx video-conferencing service in Cisco’s AWS account.. 5 months after leaving the company.
- Sendgrid Under Siege from Hacked Accounts by Brian Krebs: e-mail service provider Sendgrid is grappling with an unusually large number of customer accounts whose passwords have been cracked, sold to spammers, and abused for sending phishing and email malware attacks. Sendgrid’s parent company Twilio says it is working on a plan to require multi-factor authentication for all of its customers, but that solution may not come fast enough for organizations having trouble dealing with the fallout in the meantime.
💻 Programming
- Python
mmap: Improved File I/O With Memory Mapping by Luke Lee: usingnmapcan provide significant performance improvements in code that requires a lot of file I/O. This tutorial, you will learn how to use memory mapping to read large files faster, how to change a portion of a file without rewriting the entire file and how to usemmapto share information between multiple processes.
🐧 Linux
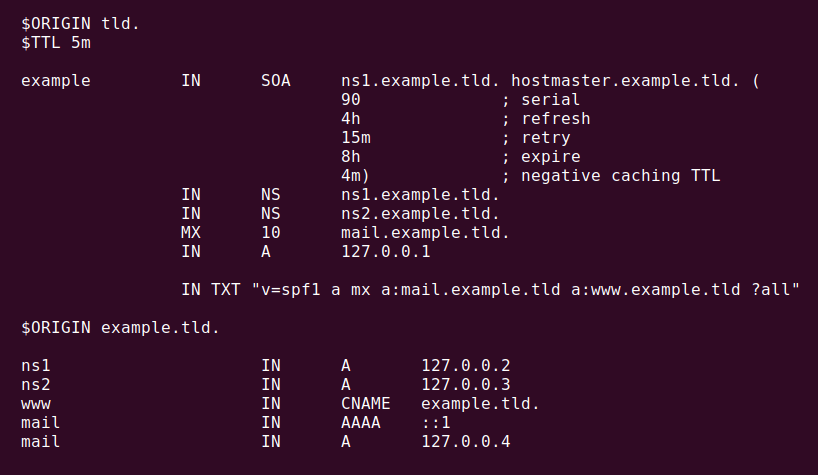
- Understanding DNS: anatomy of a BIND zone file by Jim Salter: need a clear, thorough guide to understanding how DNS records work? We got you.
- Supporting Linux kernel development in Rust: the Rust programming language has long aimed to be a suitable replacement for C in operating-system kernel development. As Rust has matured, many developers have expressed growing interest in using it in the Linux kernel. At the 2020 (virtual) Linux Plumbers Conference, the LLVM microconference track hosted a session on open questions about and obstacles to accepting Rust upstream in the Linux kernel - this article captures the main points of that discussion.
🚢 Leadership
- Camille Fournier on Effectively Managing Internal Platform Teams by Matt Campbell: Camille Fournier, managing director, head of platform engineering at Two Sigma, recently shared her learnings from managing internal platform engineering teams. Two of the key challenges she shared are the smaller size of the customer base and the challenge in understanding how your customers will use your product. She also stressed the importance of ensuring invested development work is aligned to the best interests of the product and the end user.

- Managing Remotely: 6 Ways to Support Engineers by Ravs Kaur: our shift to remote work in 2020 moved the majority of face-to-face interactions into screens. Although initially we assumed this shift was a temporary adjustment, most of us now realize it’s just the opposite. As a result, managers—the forgotten middle of the workforce—are emerging as quiet heroes fighting to protect team effectiveness.
☁️ Cloud
- Reserved Instances: The Complete Guide by Zev Schonberg: reserved instance strategies compared across the big 3 cloud providers (AWS, Azure, GCP).
AWS
-
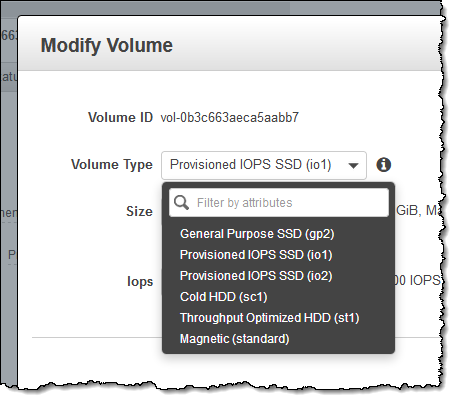
New EBS Volume Type (io2) by Jeff Barr: 100x higher durability and 10x more IOPS/GiB at the same price as the existing io1 volumes.
-
SNS launches client library supporting message payloads of up to 2 GB: Simple Notification Service (SNS) now has launched an open-source Extended Client Library for Java that enables you to publish and deliver messages with payloads up to 2GB. Previously, message payloads were supported up to 256KB.
-
Amazon EKS managed node groups now support EC2 launch templates and custom AMIs: until now, you could only provide a limited set of instance level customization options through the managed node groups API. With the launch template integration, you can customize a wide range of EC2 instance settings to meet compliance and application requirements, while offloading the operational tasks of node provisioning, draining, and upgrading to EKS.
-
Bottlerocket goes GA: AWS announced the General Availability of Bottlerocket, a new open source Linux-based Operating System (OS) purpose-built to run containers that only includes the software needed to run containers and comes with a transactional update mechanism. These properties enable customers to use container orchestrators to manage OS updates with minimal disruptions, enabling improved security and lower operational costs for containerized applications.

- AWS Tagging Best Practices Guide: Part 2 (Enforcement) by Karl Hughes: once you have adopted an AWS tagging strategy, you’ll need to make sure that all your existing AWS resources and any new ones you create abide by it. Consistency is the key - if you don’t proactively enforce your AWS tagging strategy, you’ll always be playing catch up and chasing down team members to make sure they add the right tags to their resources.
Article version: 1.0.0